One agent or a thousand.
The amnesia is the same.
Adaptive memory for one agent or an entire fleet.
Identity Plane
One adaptive memory per agent. Cross-session attacks stop being invisible.
- Memory, not classification — identity built from compressed behavior across every session
- Trajectory detection — drift, injection, exfiltration caught before the pattern completes

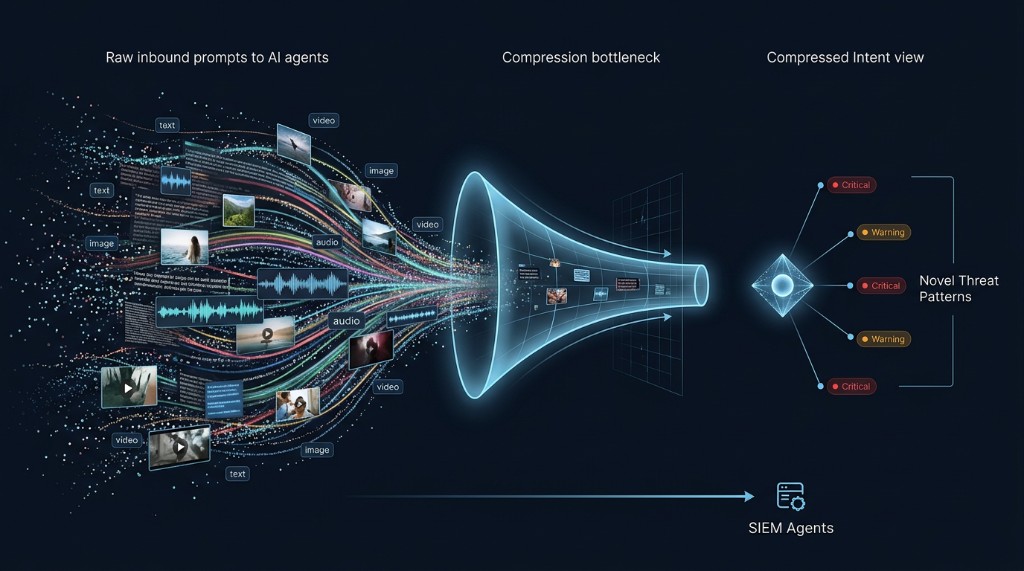
SIEM-less Detection
Fleet-wide threats, no data lake. Each request looks normal alone. Together, they're a coordinated campaign. One shared memory across the fleet makes the pattern visible.
- Shared fleet memory — millions of prompts compressed into one cohesive story
- Coordinated attack detection — campaigns surface even when every individual request passes
Computation Behavior Analytics
Prompt injection is inevitable. Every inbound prompt induces a computation signature. We remember them across every agent and prompt. Unusual prompts surface against the baseline.
Define your agents. Detect drift.
Describe what your agents should do in plain language. Everything that doesn't fit gets surfaced.
- Org identity profile — natural-language description of sanctioned agent behavior
- Intent divergence, not rules — deviation from modeled identity, so novel threats surface automatically
"Sustained pressure to initiate trade orders outside its read-only mandate. Recurring attempts to disable pre-trade risk checks. Identity is being displaced toward unauthorized order execution with suppressed audit visibility."
Lossless memory. Bounded size.
A fleet generates millions of prompts. Most are noise. Agentic SIEMs decouple compute from storage and let agents figure it out. That gets costly. Intrinsec's memory gives your SIEM a curated starting point. Agents work less. Costs drop.
- Deduplicate to novelty — 10,000 identical probes become one pattern and a count
- Fragment-level extraction — captures the 50 threat tokens, not the 2,000-token prompt